Gartner estimates that SD-WAN today has less than 5% market share. But, it predicts that up to 25% of users will manage their WAN through the software within two years. SD-WAN sellers’ revenues are growing at 59% annually. According to Gartner estimates, it is expected to become a $ 1.3 billion market by 2020.
Table of Contents
What is SD-WAN?
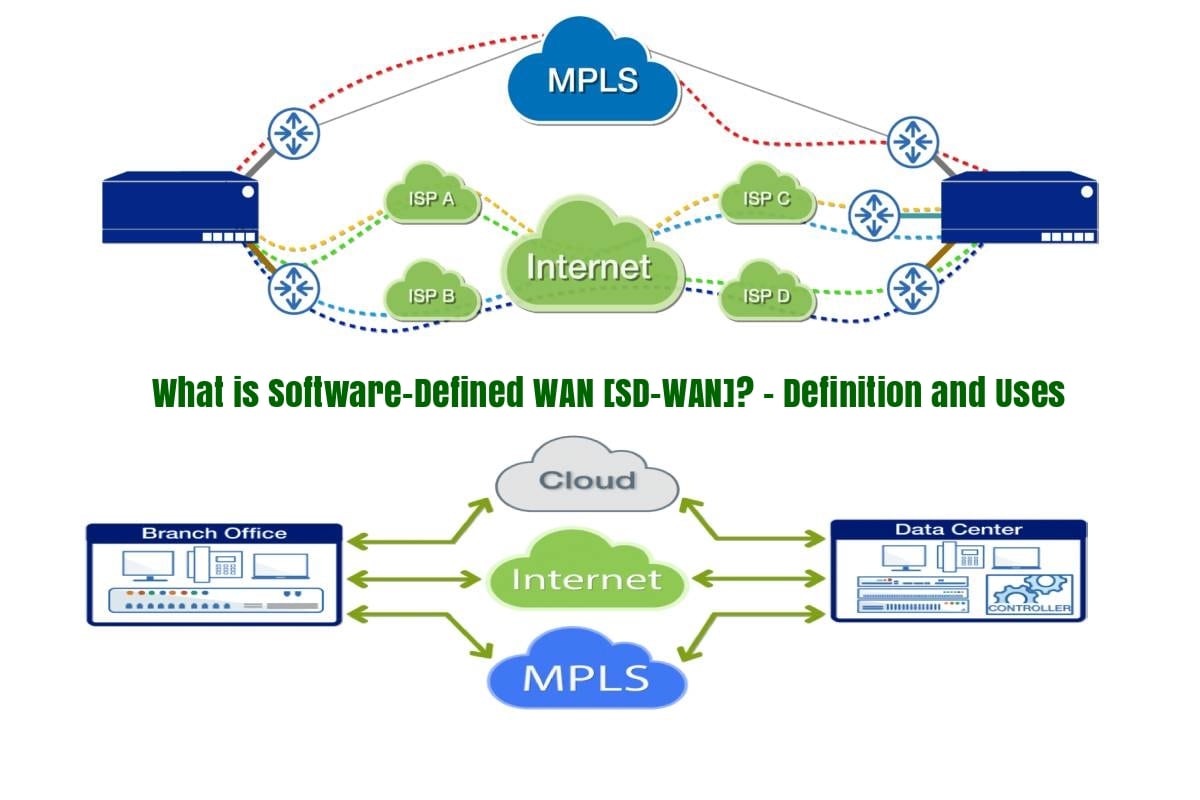
SD-WAN is an acronym of Software-Defined WAN is defined as a program that simplifies branch networks and optimizes the performance of applications on the Internet and hybrid WAN. SD-WAN originate from software-defined networks, which unlink network-based software services from the underlying hardware.
What is SD-WAN Technology?
SD-WAN is the third generation network, after IPsec (Internet Protocol Security) and MPLS (Multi-Protocol Label Switching). This technological breakthrough makes it easy for the following:
- To create or evolve your corporate network around the world.
- Build corporate network with its remote institutions, partners, and cloud providers.
- And also using any local Internet Service Provider.
- Using SD-WAN corporate network can connect to any technology, wired or wireless.
Why Use SD-WAN?
Why Corporate should use SD-WAN? This is a common question in the networking industry. We have listed the perfect reasoning for why businesses should use SD-WAN.
SD-WAN adoption is increasing rapidly because of its huge benefits
What are the benefits of SD-WAN?
Below are the major benefits of SD-WAN businesses has experienced after using it:
- Power the agility for the business, given the rapid deployment of WAN services to remote offices. And this happened without the need to send IT personnel.
- Elasticity in the bandwidth, since it can be added or reduced easily depending on the needs of the business.
- It facilitates the saving of the bandwidth and make sure connection to the Internet is available easily and quickly deploy-able. And also with much lower costs than the equivalent in MPLS networks.
- Software Defined WAN offers the reliability and security benefits of WAN services at the “Internet price.”
- It provides an architecture optimized for cloud. Because it eliminates the inconveniences and traditional penalties of MPLS networks and equates the security and performance. And also connectivity between the office and the cloud. This connectivity is considerably improves the experience of users in remote offices, when they are using SaaS applications.
- It facilitates the migration to hybrid networks. Most distributed organizations have MPLS deployed in remote offices. Companies can deploy SD-WAN solutions without changing existing networks.
- It allows the automation of traffic management when prioritizing traffic. The key is to provide network managers with easy-to-use tools for prioritizing features. And that to automate changes in traffic flows based on actual network conditions.
How to Use SD-WAN?
SD-WAN can be used in different ways. We are going to discuss the basic deployment guide of SD-WAN. We also discuss advantages of deployment with the deployment guide.
How to Deploy SD-WAN?
Digital transformation is much more than moving workflows to the cloud and adopting the Internet of Things (IoT). It is about reorganizing the entire network to make it faster, more efficient, much more flexible and profitable. This means that it also includes incorporating agile software and application development. Rethinking access and integration, and creating dynamic and adaptable network environments.
With the growing trend of using cloud-based applications, the SD-WAN Deployment in companies becomes more relevant. Check out the Top 3 SD-WAN Deployment Consideration in 2019.
Advantages of SD-WAN Deployment
SD-WAN Deployment has many advantages, we will discuss few of them:
- SD-WAN Deployment has a much lower risk of security, downtime, reliability, and Quality of Experience (QoE).
- SD-WANs also allow for easier network administration, which helps to update network performance, predictability, and quality of service.
- The work of the IT team is simplified, thanks to the centralized configuration and organization. The centralized configuration eliminates the need to configure and update each branch device separately. It offers the possibility of consolidating branches, reducing the number of devices that are managed in the branch. It happens by incorporating routing, WAN optimization, and firewall capabilities.
- You can also solve the problems in fractions of a second and then notify the network administrators, instead of tracking and fixing them manually.
- On the other hand, SD-WAN generates cost savings primarily by leveraging low-cost broadband to increase or replace MPLS connections.
- SD-WANs contribute positively to the return on your IT investment.
Also Read: What is a Router?
How Many SD-WAN Vendors?
Software-Defined WAN delivers great performance and exceptional experience for SaaS, cloud and virtual applications at all times. It also helps increase agility, reduces network costs and provides visibility into network performance.
Check out the complete details of the Top 5 SD-WAN Vendors globally, which includes their definition, features and uses:
What is Cisco Meraki SD-WAN? – Definition, Features and Uses
What is Cisco Viptela SD-WAN? – Definition, Features and Analytics
What is VeloCloud SD-WAN? – Definition, Architecture and Functions
What is Silver Peak SD-WAN? – Definition, Features and Advantages
What is Nuage SD-WAN? – Definition, Features and Uses
What is Riverbed SD-WAN? & Why to Choose It?
What are the SD-WAN Features?
Technology that makes up SD WAN is not new, the concept is formed by the “package” that makes it up. There are many SD-WAN Features, where as according to Gartner it has four characteristics:
- It must support multiple types of connection: MPLS, Internet, LTE, etc.
- You can make a selection of dynamic routes: Allows load balancing through WAN connections.
- It provides a simple interface for running the WAN. And it must support “zero-touch” provisioning in a branch office and in a way as simple as configuring a home Wi-Fi connection.
- It must support VPN, third-party services such as WAN optimization controllers and security services. Security services such as firewalls, perimeter gateways, etc.
What is SD-WAN Architecture?
When you start a day with a series of deliveries and to deploy a secure SD-WAN architecture. You need to have keys for deliveries and deployment of SD-WAN architecture. Here are the Keys that take into account aspects such as security and deployment. And how to segment applications for better control.
What is most interesting when deploying any architecture, whatever the type? Safety. It is a premium condition above all things, so it is vital to give it the attention it deserves.
So, in the case of SD-WAN, how can you not dedicate a few minutes before performing the desired deployment with this technology?
Because what is clear is that moving from a traditional WAN architecture to another defined by software (SD-WAN) results in an improvement in security. Especially in an environment where business agility is required for remote sites to run quickly.
What are the Values of SD-WAN?
A key value of SD-WAN is that it unifies secure connectivity in all transports without losing their independence. Therefore, it is not necessary to use a different security mechanism for different types of transport. Or, to depend on the transport provider for your secure network.
Also, another aspect to keep in mind: the network overlay can support a wide variety of security capabilities. That said, here are the main requirements that should be in each Software-Defined WAN security checklist.
And in the face of these investment needs and priorities, budgets are not shared equally. As IDC said in the session, it does for Digital Transformation, to migrate to public cloud services.
But all this requires increasing the connectivity, bandwidth, and performance of critical applications. Applications which run through these networks has a continuous act of balancing to respond to these needs when the budget does not grow.”
What are SD-WAN Segmentation?
SD-WAN can perform a deep recognition of applications, which allows very granular control over how specific traffic is routed
Most companies today need for segmentation to isolate different types of traffic for regulatory reasons. For example, PCI data, or to provide their network segments to different business groups. Companies can address these needs in the same way that a service provider would use virtual routing and forwarding (VRF).
Secure insertion of services
An SD-WAN solution will incorporate basic security features. Such as, a next generation Layer 7 firewall in edge devices. But, it will not necessarily be a first-class security solution. However, additional security services can be inserted in multiple locations as needed to provide all the security capabilities and business needs.
Also Read: What is a Data Center? – Definition and Uses
What is SD-WAN Infrastructure?
Many companies have complex infrastructure in their branches, consisting of routers and WAN route controllers. Also, includes WAN optimizers, firewalls, and other components. It is expensive to buy and maintain and complex to administer.
Lerner estimates that an SD-WAN can be up to two and a half times less expensive than a traditional WAN architecture.
It is estimated that a WAN of 250 branches in three years costs 1.28 $ 5,000 in a traditional WAN architecture and only 452,500 with an SD-WAN deployment.
The ability to use routers is the biggest savings, along with staffing and a small decrease in router maintenance and support.
This ease of deployment, central administration, and reduced costs make Software-Defined SDN WAN an attractive option for many companies.
But if SD-WAN is so good, why is not it more ubiquitous? Many organizations have ASICs built as they control their WANs and LANs, which have long refresh cycles. Network engineers are also traditionally reluctant to drastic changes.
How is SD-WAN Cost Calculated?
Software-Defined WAN is the answer to the reduction of costs compared to the traditional networks of the MPLS operators. Being able to achieve a reduction of up to 48% in the interconnections between offices or branches.
The benefits of SD-WAN are already a reality, and this is contrasted by Gartner, in its report where it is estimated that by 2019 it will be implemented in 30% of companies, in 2016 only 1% enjoy it.
So, what does it give us?
-
- It gives greater bandwidth at a lower cost. SD-WAN unite MPLS and multiple low-cost broadband routes in a hybrid cloud.
- Greater reliability in critical applications such as VDI, application virtualization and VoIP. It also includes video conferencing, video surveillance, intercom, ERP, and CRM compared to others.
- Simplified administration. The deployment of SD-WAN is very fast, and its administration is simpler to be centralized and not depend on the support in each delegation.
MPLS networks generally offer highly reliable packet delivery. Internet links, on the other hand, often fail.
To compensate for this fact, many organizations that move completely to the SD-WAN choose to request multiple Internet links. These multiple internal links are from different providers to maintain the availability of “four nines” (99.99 percent) in the case of failure of the link.
Is SD-WAN Secured?
The availability of applications and their performance depends, to a large extent, on the capacity of the network. The arrival of software-defined WANs has accelerated this capacity, but a new concern has also opened up that should not be dismiss by any company. Companies which thinks about its Digital Transformation, will surely thinks about SD-WAN security.
Organizations Security
Organizations have raised their awareness of this problem and seek security in all technologies. Technologies that they implement in their organization, and it cannot be less in their Software Defined WAN networks.
Businesses are seeing how their business models change thanks to the use of innovative technologies. Today, 92% of companies, according to an IDC survey, consider Digital Transformation as one of the keys to their strategy.
This transformation involves reconsidering how business is running. But also, how businesses are increasing their growth. Applications, connectivity, have become key to developing daily activity. And therefore, all means must be put in place to guarantee users. Regardless of, where they are located, that they will be able to work with their data. And also their business applications, Quickly and safely.
Third Platform Security
“It is necessary to understand the possibilities of the third platform: cloud, big data, mobility and social.” Explains Ricardo Malhado, Senior Research Analyst of IDC, in the webinar “SD-WAN, how to guarantee your security?”.
It is in the third platform where is the global spending on ICT, and in the accelerators of innovation: robotics, IoT, cognitive systems, and augmented reality “.
However, there are also challenges. Challenges such as, “each pillar of the third platform is a factor of exposure to risk.” According to an IDC survey on business communications in which participants were ask about the main IT or network risk. Many said that, in the next two years, security was the most mentioned.
CyberAttacks
The concept of security perimeter has disappeared and the attack surface increases. The number of threats increases daily. Also, we assist in the professionalization of hacking and offer itself as a service. Whereas criminals who act as open source communities, share the threats collaboratively.
It is a global phenomenon that is increasingly difficult to combat. It changes the notion of business priorities.
The IDC numbers confirm the change in priorities, which is noticeable in just one year. “In 2016, the priorities of technological investment did not include security or virtualization of the network. In 2017 they were concerns within the top 5, “says Machado.
The greatest concern for the security of the network is due to an “urgent context regarding the need to be compliant with GDPR. While the investment in network virtualization is because companies realize that Networks are a barrier to achieve business objectives.
Also Read: 13377x Torrent – Download Movies, Games, Software, Music and More
What is the difference between SD-WAN vs SDN?
SD-WAN and SDN are the small brothers of the networks defined by software. They are similar, both defines by software. But, SDN is intended for internal data centers in a headquarters. Whereas SD-WAN takes those similar software-defined concepts and decoupling the plane of control from the data plane to the WAN. “SDN is architecture, while Software-Defined Wide Area Network is a technology that you can buy,” explains Andrew Lerner, an analyst at Gartner.
One of the main features of SD-WAN is its ability to manage multiple types of connections – from MPLS to broadband to LTE.
Managing a WAN through the software provides useful benefits. Any problem is notified and can manage all your WAN through a single interface. Recently, making changes to the network configurations in the branches would have required the creation and installation. Installation of manual configurations probably a technician on the site to do so.
If a company decided to extend the teleconference to its branches, for example, the predefined bandwidth allocations would have to be restructured. It may be necessary to acquire more bandwidth, then program it and install it at each location in the branch.
What is difference between SD-WAN vs MPLS?
Before the arrival of the SD-WAN, there was the switching of multiprotocol labels, better known as MPLS. Multiprotocol tag switching is a way to ensure reliable connections for real-time applications by establishing predetermined. And highly efficient routes once a packet enters the network.
Each of these technologies presents its pros and cons. Compilation of the most significant advantages and disadvantages of each you can decide which network traffic protocol technology. This technology is most convenient for the organizations. Check below SD-WAN vs MPLS what technology to choose.
What are pros and cons of MPLS
When compared to MPLS, software-defined wan has more reliable and secure. As a technology experts we recommend SD-WAN as a better choice.
Pros of MPLS
- One of the most important characteristics of MPLS is the reliable delivery of packages. Packages that transport real-time traffic, such as voice over IP (VoIP) or video, can be easily assigned to low-latency routes throughout the network, something difficult with conventional routing. It makes the experience for the end user optimal.
- The MPLS works similarly to switches and routers, located between layers 2 and 3. It uses technology to send packets and labels to make decisions about data forwarding. The label imposes between layer 2 (data link) and layer 3 (network) headers. It makes the MPLS reliability possible by virtually isolating the packets.
- Also, MPLS providers can assign a higher priority to certain network traffic. These benefits provide a sense of traffic predictability within the network. Network routes are predetermine, so packets travel only along the routes they have been assign. It allows for better performance, better bandwidth utilization, and a reduction in network congestion.
Cons of MPLS
- On the other hand, although the MPLS network consider as secure, it does not provide encryption. And, if implemented incorrectly, can open the network to vulnerabilities.
- It is undeniable that SD-WAN offers many more advantages over MPLS. Companies are looking for alternatives to MPLS due to their high cost, limited bandwidth, extended waiting time, and extended contract terms. And Internet links are an attractive option.
Conclusion
SD-WAN expands bandwidth and provides direct and efficient access to applications (corporate and in the cloud) and data. In addition, it allows to implement virtual services – both local and in the cloud – and considerably optimize operational automation.
Companies want to innovate, generate new services and new business models. And also reduce costs and can be more agile. Networks are increasingly complex and expensive to monitor. Also, their security is more complex and difficult to scale.
Also Read: What is $GetCurrent & How to Delete it in Windows 10? [Tutorial]
Additional Resources:
SD-WAN Deployment – Top 3 Considerations in 2019
What is SD-WAN Architecture? – Definition, Types, Benefits and Uses
SD-WAN vs MPLS – Difference, Pros, Cons and Right Choice
SD-WAN Benefits Explained

![SD-WAN [Software-Defined WAN] Definition What is SD-WAN?](https://www.computertechreviews.com/wp-content/uploads/2019/05/SD-WAN-Definition-1024x683.jpg)