Kamran Sharief
What is Imperva? – Definition, Its Features and More
What is Imperva? Imperva provides powerful security products targeted at Web applications, databases, and file servers targeted by attackers. In…
Your Best iTunes Alternative for iPhone Data Management
Best iTunes Alternative for iPhone Data Management Each apple user accepts the fact that iTunes is a big mess. There…
What is Whitelisting? – Definition, Applications, and More
Whitelisting Definition A whitelisting is of email marketing, refers to all those emails, IP addresses, and domains. That also considers…
What is Okta? – Definition, Features, Okta Adaptive MFA and More
Okta Definition Okta is a cloud application security, which is a world-class Identity Management service compatible with local and mobile…
What is njRat? – Definition, How was it introduced and More
njRat Definition njRat is a program cataloged as a remote access Trojan. If installed, it runs in the background without…
Features of a Reliable Internet Connection: What to Look for Before Purchasing
Living in a connected world demands a reliable, stable and fast internet connection. With the advancement in technology, the speed…
Zen Reborn Babies can improve Digital Marketing
Babies are really fond of their Zen Reborn Dolls that will give them lots of choices through digital marketing strategies….
What is AES? – Definition, Features, Uses and More
AES Definition The AES (Advanced Encryption Standard) is one of the most common methods of encrypting essential data, which organizations…
Want to become a photographer? Here’s what you should know
How to Become a Photographer? Is photography a profession or a hobby? Of all the careers and hobbies that exist,…
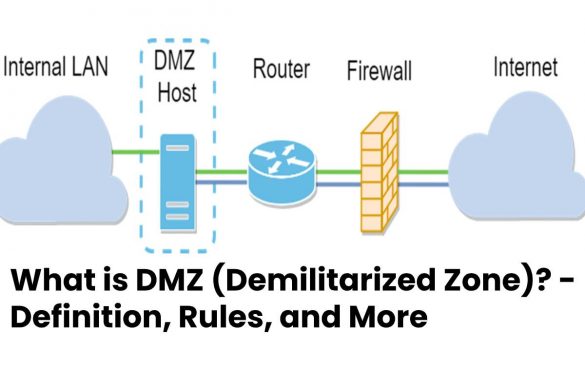
What is DMZ (Demilitarized Zone)? – Definition, Rules, and More
DMZ Definition The DMZ (Demilitarized Zone) is an independent network that acts as a buffer zone between an external network…
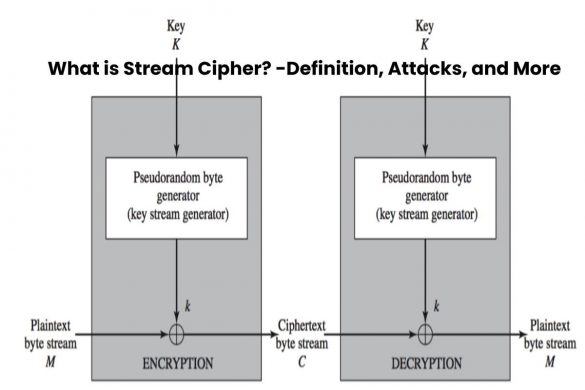
What is Stream Cipher? – Definition, Attacks, and More
Stream Cipher Definition A Stream Cipher is an encryption method and is part of symmetric cryptography. With stream ciphers or…
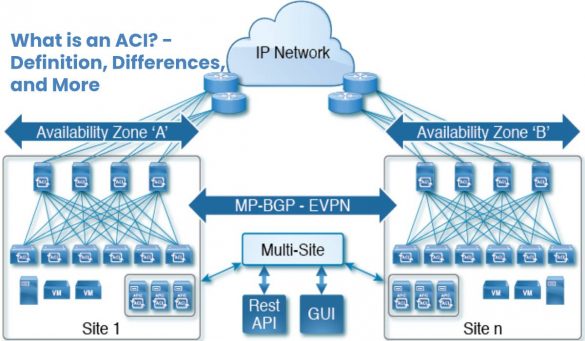
What is an ACI? – Definition, Differences, and More
ACI Definition With ACI (Application Centric Infrastructure), the data center network can be optimized-including components from other manufacturers. The design…
Recent Posts
How much dirt does your video game console accumulate?
How much dirt does your video game console accumulate The video game industry has exploded because of the pandemic, as…
How To Easily Restore Damaged WordPress Core Files
How To Easily Restore Damaged WordPress Core Files WordPress is a brilliant CMS that, 99.99 percent of the time, provides…