Kamran Sharief
What is ATP (Advanced Threat Protection)? – Definition and More
ATP Definition ATP (Advanced Threat Protection) provides security alerts for unusual activity so customers can detect and respond to potential…
What is MICR? – Definition, Quality, Benefits, and More
MICR Definition Magnetic ink character recognition code, known as MICR, is a character-recognition technology used mainly by the banking industry….
What is a VirusTotal? – Definition, Advantages and More
VirusTotal Definition VirusTotal is a web and a tool. Created by the Spanish security company called Hispasec Sistemas — despite…
What is Cryptography? – Definition, Types, and More
Cryptography Definition Cryptography is the science and art of writing messages in encrypted form or code. It is part…
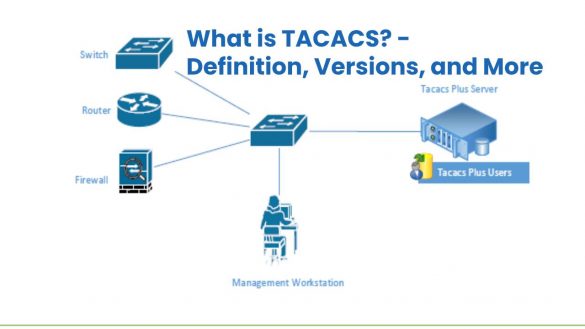
What is TACACS? – Definition, Versions, and More
TACACS Definition TACACS is known as Terminal Access Controller Access Control System, is a remote protocol used to link with…
What is a Penetration Test (Pen test)? – Definition, Methods and More
Penetration Test Definition A penetration test (pen test) is a test to check the security of a computer system through…
What is Wireshark? – Definition, Uses, Features and More
Wireshark Definition Wireshark is a multiplatform tool with a graphical interface for network analysis, a product of Ethereal’s evolution. It…
What is a UTM (Unified Threat Management)? – Definition and More
What is UTM? UTM (Unified threat management) is an information security term that refers to a single security solution. And,…
What is a Macro Virus? – Definition, Types, and More
Macro Virus Definition Macro Virus adds their code to the macros contained in documents, workbooks, and other data files. The…
What is MAC [Message Authentication Code]? – Definition, and More
MAC Definition A MAC (Message Authentication Code) used to obtain certainty about the origin of data or messages and their…
What is a Personal Firewall? – Definition, Types, Safety, and More
Personal Firewall Definition A Personal firewall is a protective measure against foreign and unauthorized attempts to connect from the public…
What is Time Based One Time Password (TOTP)? – Definition, and More
TOTP Definition The TOTP process is an extension of the HOTP, which generates a unique password by taking the uniqueness…
Recent Posts
How much dirt does your video game console accumulate?
How much dirt does your video game console accumulate The video game industry has exploded because of the pandemic, as…
How To Easily Restore Damaged WordPress Core Files
How To Easily Restore Damaged WordPress Core Files WordPress is a brilliant CMS that, 99.99 percent of the time, provides…





![What is MAC [Message Authentication Code]? - Definition, and More](https://www.computertechreviews.com/wp-content/uploads/2019/12/maxresdefault-2-585x390.jpg)



