Top Five Features For Your Business’s Security System.
Top Five Features For Your Business’s Security System One of the most brilliant elements of a security system is that…
Where Having a Home Safe Can Save the Day
When life throws unexpected challenges your way, understanding how a home safe can save the day becomes glaringly obvious. From…
What Are Cloud Storages And Which Are Best To Store Data
Every business regardless of its size generates huge amounts of data every day. Data is one of the most important…
What are the Key Differences Between UX and UI Design?
UX design and UI design are so often used together that people started to use them interchangeably, but this is…
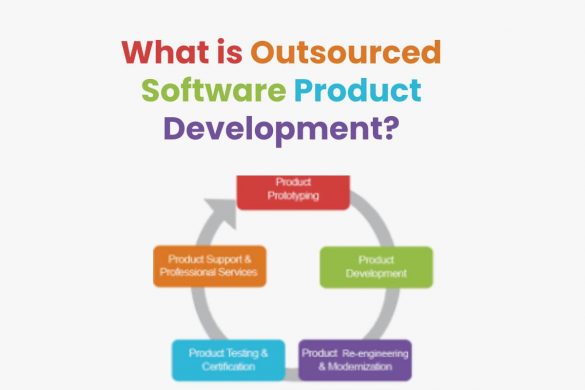
Outsourced Software Product Development in Detail [2026]
Outsourced Software Product Development is one of the types of engineering services, within which certain applications are developed that companies…
Why Bitcoin is Banned in Most of the Countries and What is the Future of the Bitcoin
Why Bitcoin is Banned in Most of the Countries Get started with online digital currency and learn useful tips and…
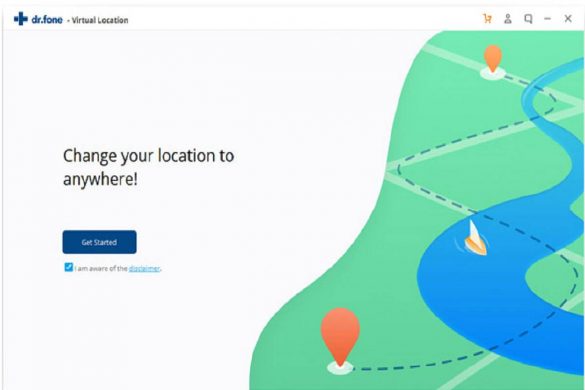
How to Safely Spoof the Pokémon go with Dr.fone – virtual location?
A lot of mobile apps and games are out there that run based on the location that can be used…
Hiring a Podcast Manager Is the Smart Move for Podcasters
Hiring Podcast Manager Is the Smart Move for Serious Podcasters Podcasting is becoming more and more popular, and many people…
Three Advantages of CNC Milling
Advantages of CNC Milling – CNC milling is one of the CNC machining services that is available. This is a…
Ensuring Compliance in Complex Cloud Architectures
Ensuring Compliance in Complex Cloud Architectures As businesses continue to embrace the advantages of cloud computing, the complexity of managing…
Leverage Collective Intelligence to Drive Improvements
In the ever-evolving quest for progress and excellence, organizations are constantly seeking fresh avenues to nurture innovation and drive continuous…
CEH Certification: Proficiency in Ethical Hacking Techniques
CEH Certification: Proficiency in Ethical Hacking Techniques A certified Ethical hacker is one of the most reputed and respected job…
Recent Posts
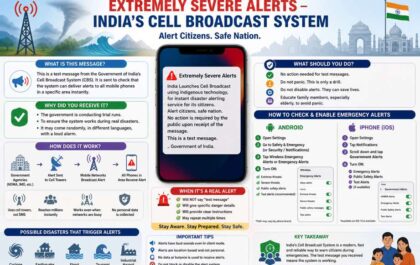
Extremely Severe Alert – A Message From Indian National Disaster Alert System
May 02nd, 2026 Extremely Severe Alert Message from Indian National Disaster Alert System has shocked every citizens. That message is…
What is Litecoin? – Definition, Functions, Properties, And More
Definition Litecoin Litecoin was a bitcoin spinoff or altcoin, starting in October 2011. It is a peer-to-peer cryptocurrency and open-source…