Kamran Sharief
3 Critical Levels of Defense Against Malware
Defense Against Malware There is malware threatening your device right now. In fact, the forces of cybercrime never stop attempting…
Why Trucking Companies Need A Fleet Management Software?
Let us begin by defining what a fleet management software is and what it does. The most basic function of…
What do you need to Become a Scrum Master?
The role of the software in every industry is very vital to the smooth running of the business of the…
What is Snapchat? – Definition, Functions, Terms and More (2023)
Definition Snapchat [Snapchat] is multimedia messaging (Text, sound, and still or animated graphic image) app used throughout the world, created…
Top 7 Applications of C Programming
C can be classified as a general-purpose, middle-level, programming language, and finds use in applications across multiple domains. As a…
What is Insider Threat? – Definition, Protection Against them and More
Insider Threat Definition Insider Threat is a kind of risk posted by all internal employees and people who have access…
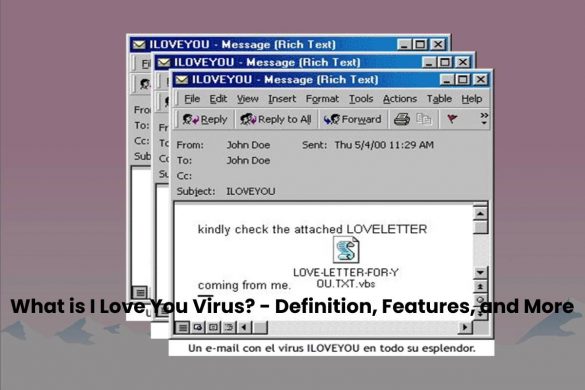
What is I Love You Virus? – Definition, Features, and More
I Love You Virus Definition The computer, I Love You Virus. Known to users as the ” Love Virus, “it…
What is Kerberos? – Definition, Elements and More
What is Kerberos? Kerberos is an authentication protocol, but not an authorization one. This means that the protocol is responsible…
What is Phishing? – Definition, Methods, and More
Phishing Definition Phishing describes the attempt to steal identifiers and passwords via the Internet by sending fake emails or SMS….
What is TAN [Transaction Authentication Number]? – Definition, and More
TAN Definition TAN stands for the Transaction Authentication Number. You usually need a TAN for all banking transactions that you…
What is the SOC? – Definition, Advantages, and More (2023)
SOC Definition The Security Operations Center, abbreviated SOC, is the center for all security-related services in the IT environment of…
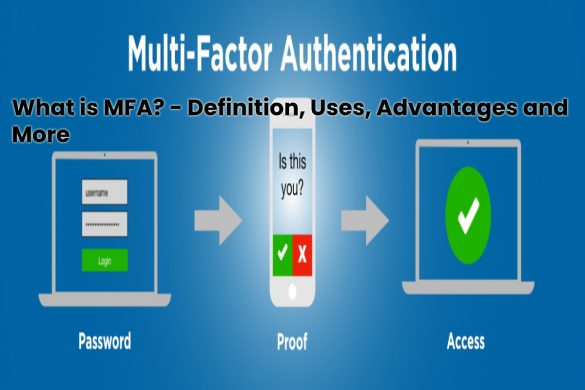
What is MFA? – Definition, Uses, Advantages and More
What is multifactor authentication? MFA, or Multi-Factor Authentication, is a security process that requires multiple authentication methods to access a…
Recent Posts
Sharing HEIC Files: Why Your Friends Can’t Open Your Photos
For many of you, taking pictures is a real pleasure. The desire for professional and high-quality photography also requires investing…
7 Ways to Enhance Your Soundbar Setup
The idea of buying a Mivi soundbar is fantastic, as it will allow you to evolve your home audio experience….






![What is TAN [Transaction Authentication Number]? - Definition, and More](https://www.computertechreviews.com/wp-content/uploads/2020/01/New-Project-55-585x390.jpg)