Table of Contents
I Love You Virus Definition
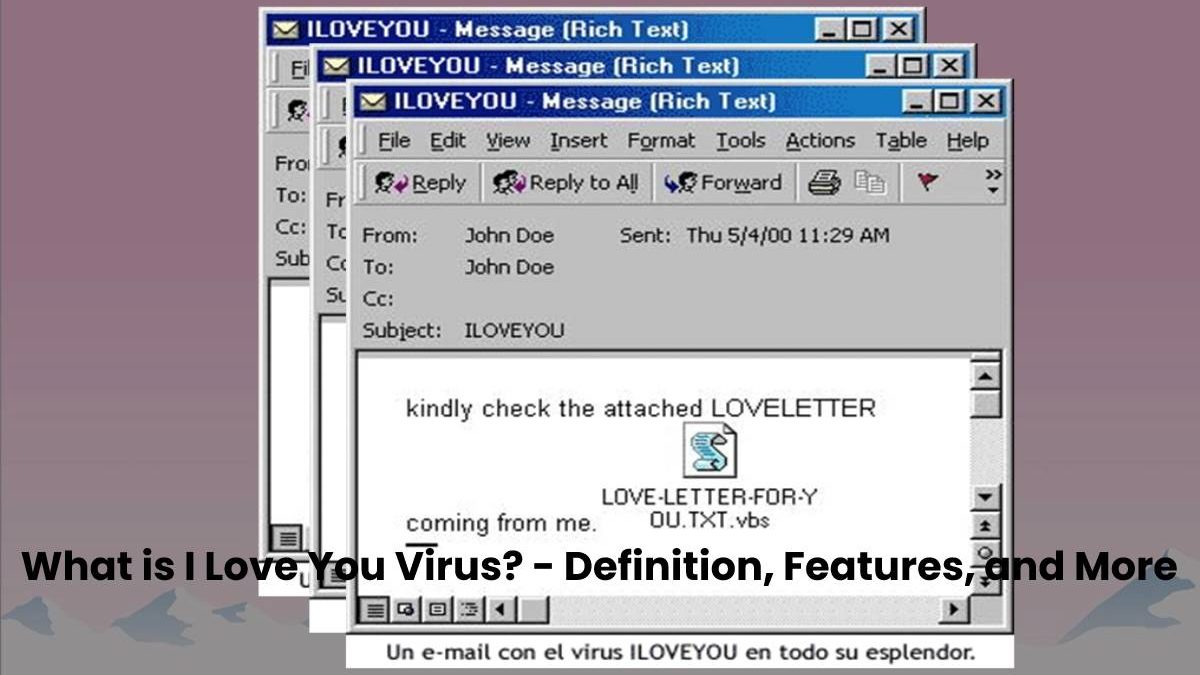
The computer, I Love You Virus. Known to users as the ” Love Virus, “it belongs to the worm category, capable of reproducing through electronic networks.
And also, modifying the files of the infected computer and transmitting it via email when the Internet user opens the file where he stays.
On May 4, 2000, this virus released on the network, quickly filling up the more than 3 million computers.
I Love You Virus was released in the Philippines, making Asia the first country to suffer from its destructive effects, followed by Europe and Russia.
Also Read: What is Phishing? – Definition, Methods, and More
What are the Features of this Virus?
The virus overwrites files with.VBS and.VBE extensions with its code. Delete the files with extensions.JS, .JSE, .CSS, .WSH, .SCT and .HTA, and create others with the same name and extension.
It locates files with the extension.JPG, .JPEG, .MP3, and .MP2, delete them, and create others where the new name is formed by the previous name.
How does this I Love You Virus work?
- After the first start of the “love message” copies itself into the system directories and the registry of the operating system and then searches the computer for multimedia files.
- When the virus found, it changes the data extension and sometimes makes it invisible to the user.
- I then start a fan mailing to the recipients and download a program to steal passwords and send information to the creator’s email address.
- However, computer viruses love letter 2000. The code has been heavily modified, and if its action previously only damaged multimedia files, everything changed over time.
- New versions of the “love message” lead to the failure of the computer, deletion and modification of the system file INI and BAT, which are responsible for loading the machine.
What are the precautions to be taken?
There are still a few versions on the Internet. Viruses are fewer because Kaspersky Lab has long been developing a program that can detect any change in the “love message.”
- The software checks the script before it runs, and if it detects any malicious code in it, it prevents the script from starting.
- But already active virus I love you (the creator of this filth, Onel de Guzmán) cannot stop – it can only delete by losing the affected files.
- In order to avoid such consequences (users who do not consider to protect their PC), it is better not to download suspicious attachments, even if they come with a letter from a friend.
- It is necessary to double-check with a friend what is in them and make sure that the email was sent by someone, not by a malicious program.
Also Read: What is Kerberos? – Definition, Elements and More