Networks Write For Us

A network is a collection of linked devices that may exchange information and resources, including computers, servers, and routers. File sharing, internet access, data exchange, and remote collaboration are all made possible by networks.
Types of Networks
1. Based on Size & Coverage
- PAN (Personal Area Network): Small network connecting devices around a single user (e.g., Bluetooth, USB).
- LAN (Local Area Network): Connects devices within a limited area (e.g., home, office, school).
- MAN (Metropolitan Area Network): Covers a city or large campus (e.g., city-wide Wi-Fi).
- WAN (Wide Area Network): Spans large distances (e.g., the internet, corporate networks across countries).
2. Based on Architecture
- Client-Server Network: Centralized servers provide resources to client devices (e.g., websites, cloud services).
- Peer-to-Peer (P2P) Network: Devices share resources directly without a central server (e.g., torrenting, blockchain).
3. Based on Connectivity
- Wired Networks: Use cables (Ethernet, fiber optics).
- Wireless Networks: Use Wi-Fi, cellular (4G/5G), or satellite connections.
Key Networking Components
- Routers: Direct traffic between networks.
- Switches: Connect devices within a LAN.
- Firewalls: Protect networks from unauthorized access.
- Modems: Convert signals for internet access.
- Servers: Store and manage data for clients.
Network Protocols & Standards
- TCP/IP: Foundation of internet communication.
- HTTP/HTTPS: Web browsing protocols.
- FTP: File transfer protocol.
- DNS: Translates domain names to IP addresses.
- DHCP: Assigns IP addresses automatically.
Importance of Networks
- Enables internet access and global communication.
- Supports cloud computing and remote work.
- Facilitates data sharing and collaboration.
- Powers IoT (Internet of Things) devices.
Network Security Challenges
- Cyberattacks (malware, phishing, DDoS).
- Data breaches and unauthorized access.
- Network congestion and latency issues.
Future Trends in Networking
- 5G & 6G networks: Faster wireless communication.
- Edge computing: Processing data closer to the source.
- AI-driven networking: Automated network management.
- Quantum networking: Ultra-secure communication.
How to Submit Your Articles?
To Write for Us, you can email us at contact@computertechreviews.com
Why Write for Computer Tech Reviews – Networks Write for Us

Search Terms Related to Networks Write for Us
- LAN (Local Area Network)
- WAN (Wide Area Network)
- MAN (Metropolitan Area Network)
- PAN (Personal Area Network)
- CAN (Campus Area Network)
- SAN (Storage Area Network)
- VPN (Virtual Private Network)
- SDN (Software-Defined Networking)
- Mesh network
- Star topology
- Bus topology
- Ring topology
- Hybrid network
- Peer-to-peer (P2P) network
- Client-server network
- Ad hoc network
- Router
- Switch
- Hub
- Modem
- Gateway
- Firewall
- Access Point (AP)
- Network Interface Card (NIC)
- Repeater
- Bridge
- Load balancer
- Proxy server
- NAS (Network Attached Storage)
- Patch panel
- Fiber optic cable
- Ethernet cable (Cat5, Cat6, Cat7)
- TCP/IP model
- OSI model
- HTTP/HTTPS
- FTP/SFTP
- DNS (Domain Name System)
- DHCP (Dynamic Host Configuration Protocol)
- SMTP (Simple Mail Transfer Protocol)
- UDP (User Datagram Protocol)
- ICMP (Internet Control Message Protocol)
- ARP (Address Resolution Protocol)
- BGP (Border Gateway Protocol)
- OSPF (Open Shortest Path First)
- VLAN (Virtual LAN)
- MPLS (Multiprotocol Label Switching)
- IEEE 802.11 (Wi-Fi standards)
- IPv4 vs IPv6
- Wi-Fi (802.11a/b/g/n/ac/ax)
- 4G LTE
- 5G networks
- Bluetooth networking
- Zigbee
- NFC (Near Field Communication)
- Cellular networks
- Hotspot
- SSID (Service Set Identifier)
- WPA2/WPA3 security
- Captive portal
- Roaming in networks
- Firewall configuration
- IDS/IPS (Intrusion Detection/Prevention System)
- DDoS attack
- Man-in-the-middle attack
- Phishing attacks
- VPN security
- Zero Trust networking
- End-to-end encryption
- Network penetration testing
- Malware protection
- Packet sniffing
- Port scanning
- Brute force attack
- Network access control (NAC)
- Two-factor authentication (2FA) for networks
- Cloud networking
- Virtual Private Cloud (VPC)
- AWS networking
- Azure virtual network
- Google Cloud networking
- SD-WAN (Software-Defined WAN)
- NFV (Network Functions Virtualization)
- Container networking
- Kubernetes networking
- Edge computing networks
- Network bandwidth monitoring
- QoS (Quality of Service)
- SNMP (Simple Network Management Protocol)
- Network latency
- Packet loss
- Jitter
- Network troubleshooting
- Ping and traceroute
- NetFlow analysis
- Syslog servers
- Network performance optimization
- Cable management
- IT infrastructure management
- 6G networks
- IoT (Internet of Things) networking
- AI in networking
- Quantum networking
- Li-Fi (Light Fidelity)
- Network automation
- Self-healing networks
- Intent-based networking
- 5G private networks
- Network slicing
- CCNA (Cisco Certified Network Associate)
- CCNP (Cisco Certified Network Professional)
- CompTIA Network+
- JNCIA (Juniper Networks Certified Associate)
- Network engineer
- Network administrator
- Network security specialist
- Cloud network architect
- Wireless network engineer
- VoIP engineer
Search Terms for Networks Write for Us
- submit an article
- submit an article
- become an author
- guest post
- This post was written by
- write for us
- submit post
- become a guest blogger
- guest posting guidelines
- looking for guest posts
- guest posts wanted
- suggest a post
- guest posts wanted
- contributor guidelines
- contributing writer
- writers wanted
Guidelines of the Article – Networks Write for Us

You can send your article to contact@computertechreviews.com
Related Pages:
Big Data Write for Us
Software Write For Us
Cloud Computing Write For Us
Computer Write for Us
VOIP Write for Us
Data Center Write for Us
Web Design Write For Us
Finance write for us
Certification write for us
Adobe write for us
IVR write for us
Motherboard write for us
Games write for us
Projector write for us
Chromebook write for us
Recent Posts
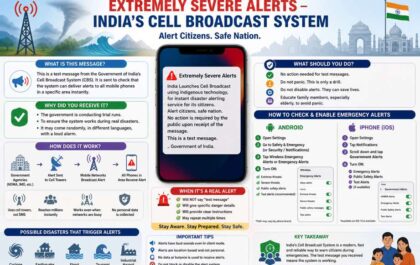
Extremely Severe Alert – A Message From Indian National Disaster Alert System
May 02nd, 2026 Extremely Severe Alert Message from Indian National Disaster Alert System has shocked every citizens. That message is…
What is Litecoin? – Definition, Functions, Properties, And More
Definition Litecoin Litecoin was a bitcoin spinoff or altcoin, starting in October 2011. It is a peer-to-peer cryptocurrency and open-source…