Streaming / cloud gaming from PC: how local rigs and remote rigs compare
As a gamer, you may need to make several decisions to get the best gaming experiences possible. It isn’t just…
The Impact of Address Autocomplete on the Checkout Process
Cart abandonment is one of the most significant challenges many e-commerce businesses experience. It occurs when potential customers start the…
A Beginners Guide to Technical SEO
Technical SEO is the method of optimizing the crawling and indexing phase of your website. You can assist search engines…
Risks of Cloud Migration: Avoid through Proper Assessment
Risks of Cloud Migration – A report states that the cloud migration services market worth will reach 448.34 billion by…
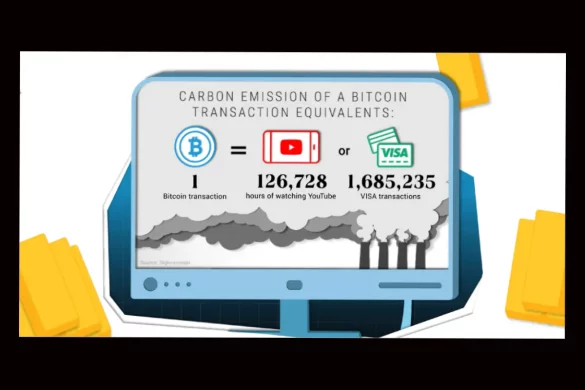
Crypto Carbon Footprint: Environmental Cost Explained [2025]
Crypto Carbon Footprint – In the age of the digital revolution, cryptocurrencies have become more than just a buzzword; they’re…
Major Credential Breaches: Account Security at Risk [2025]
Major Credential Breaches Place Account Security At Risk Imagine a traditional office environment scenario in which a different person turns…
How To Receive Passive Income: Staking Crypto
How To Receive Passive Income Staking Crypto If you know something about investing and trading, you might have heard of…
What Is 3PL and Why E-commerce Brands Businesses Need It?
What Is 3PL (Third-Party Logistics)? And Why E-commerce Brands Can’t Ignore It in 2026 Online shopping isn’t slowing down. Not…
Invest Wisely in Bitcoin: Best 5 Methods [2025]
Opportunities to invest wisely in Bitcoin are growing as it becomes more widely accepted. Investing in Bitcoin can be possible…
Photo Booth Experiences with Snappic’s Cutting
Embrace the Future of Photo Booth Experiences with Snappic’s In a world where capturing moments is as pivotal as experiencing…
IVR Systems: How They Improve the Customer Experience
Interactive Voice Response software has both supporters and opponents, but the fact remains – it is one of the most…
How To Protect Your Website From a Data Breach
As the world continues to keep up with advanced technologies, cybercriminals are becoming more tech-savvy as well. Thus, cybersecurity threats…