Table of Contents
Port Scanning Definition
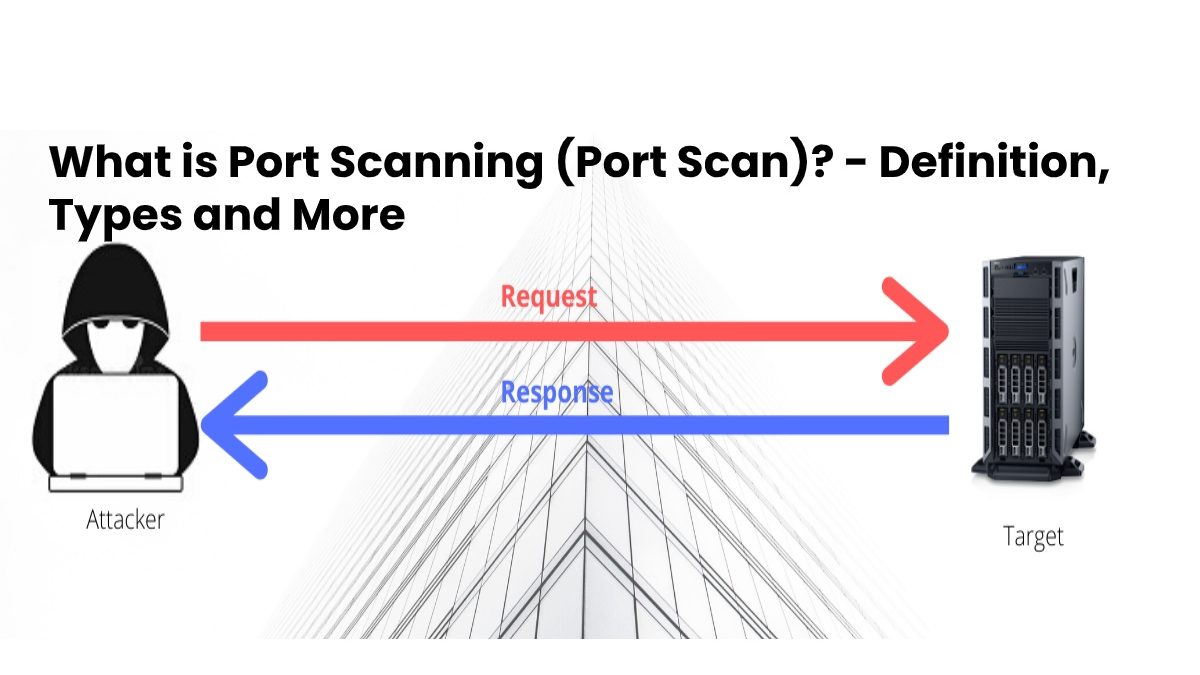
Port scanning is a process that sends client requests to a range of port addresses to a server on a host, intending to find an active port; This is not a bad process in itself.
Most users of a port scan are not attacks, but simple polls to determine the services available on a remote machine.
There are several programs to scan ports over the network. One of the best known is Nmap, available for both Linux and Windows.
Meanwhile, Portsweep is scanning multiple hosts to listen to a specific port. The latter is generally used to search for a particular service. For example, an SQL-based computer worm can scan ports looking for hosts that are listening on TCP port 1433.
This application allows you to verify the security of a computer in a network, through the analysis of its ports, locating the open ports.
And allowing the execution of an additional technique (usually an Xploit), to take remote control of the victim PC.
How does Port Scan work?
Recall that the TCP / IP ports that exist are 65,535, and each of them fulfills an international standard function.
When it carries out a vulnerability scan, what it achieves is to identify the ports that are open in a system. This is achieved by sending requests port by port and analyzing each of the respective responses.
In some cases, perhaps the most advanced ones, it is even possible to determine the use of a type of operating system on the victim machine. As well as the use of the versions of the applications for the active ports.
Types of Port Scanning
There are two methods for port scanning, one that consists of actively acquiring the information, and another passively, let’s see the difference.
Active Acquisition of Information
In this methodology, large amounts of information packets are sent, with headings that do not meet the standards, to analyze the response information.
And thus achieve the identification of the versions of the applications used to manage the data. open and active ports.
Passive Acquisition of Information
It is a non-aggressive method that, in addition to being effective, manages to evade the IDS (Intruder Detection Systems) Intrusion Detection Systems.
It works similarly to Active, performing analysis of the fields of IP datagrams that go through the network, using a port tracker.
Since the analysis performed in this way divides the values of the datagram fields, turning them into small fragments. And it takes much longer than the first methodology.
But also, it reduces even in some cases, and the possibilities will detect fully while performing the scan.
Positive Aspects of Port Scanning
The network administrators must have a port scanner at hand, to keep the infrastructure under their constant evaluation. And thus be able to solve the failures detected in time quickly.
An in-depth scan can end in an Xploit attack, and an attack of this magnitude can end in a Defacement. A Remote File Inclusion, or take full control of the server remotely.