Table of Contents
IPsec Definition
IPsec (Internet Protocol Security) is a collection of protocol extensions for the Internet Protocol (IP).
The extensions enable the encryption and information transmitted with IP and ensure secure communication in IP networks such as the Internet.
With Internet Protocol Security it is possible to encrypt data and to authenticate communication partners.
And also, It can protect the exchange of information in potentially unsafe networks such as the Internet.
Also Read: What is DNS (Domain Name System)? – Definition, History and More
What are the main features of IPsec?
The main features of Internet Protocol Security are:
- Interoperability with the world of IP protocols
- Data integrity
- Cryptographic protection by encrypting the transmitted data
- Support for various key management processes
- And also, Authentication of the communication partner
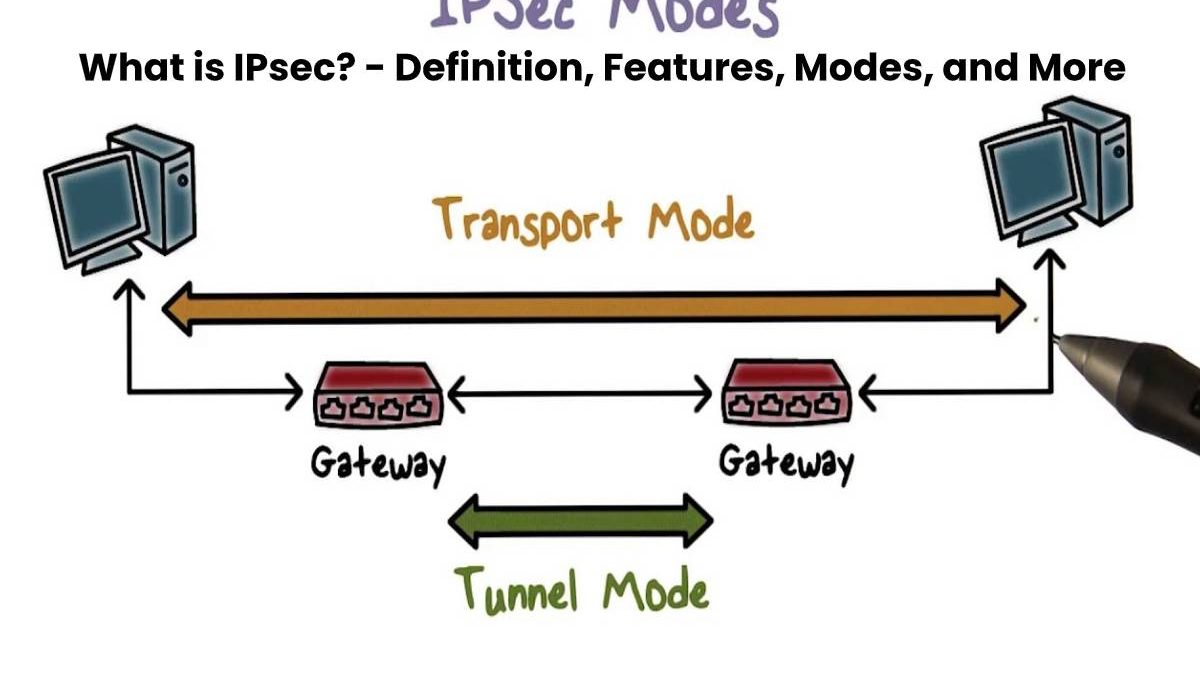
What are the different modes of Internet Protocol Security?
Internet Protocol Security has two modes:
Transport mode
- The transport mode creates a direct point-to-point connection between two endpoints.
- And also, To do this, he uses an additional IPsec header between the IP header and the transported data.
Tunnel mode
- In tunnel mode, two networks connected via a secure tunnel between two gateways or routers.
- And also, The end devices themselves connected via the two networks do not have to support Internet Protocol Security.
What are the different key management methods?
In addition to manual key management, automatic key control is possible with the Internet Key Exchange Protocol (IKE).
- IKE uses the Diffie-Hellman process for the secure generation of keys. An extension of IKE is IKEv2.
- It simplifies configuration and connection establishment. It corrects the vulnerabilities of the previous version.
- With manual key management, the keys permanently configure at the two endpoints of the encrypted connection.
What are NAT and IPsec?
In connection with Network Address Translation (NAT), problems can arise when establishing a secure connection.
- NAT gives an IP packet a new IP address and a different source port.
- The changed IP packets may result in an invalid packet for Internet Protocol Security since integrity is no longer guaranteed.
- And also, The invalid packets are discarded by IPsec and the connection establishment fails.
- To avoid the problems caused by NAT, such as IPsec pass-through or IPsec with NAT traversal, are used.
Also Read: What is SIEM? – Definition, Advantages, and More