Last Updated: April 30, 2026
Table of Contents
Attack Vector Definition
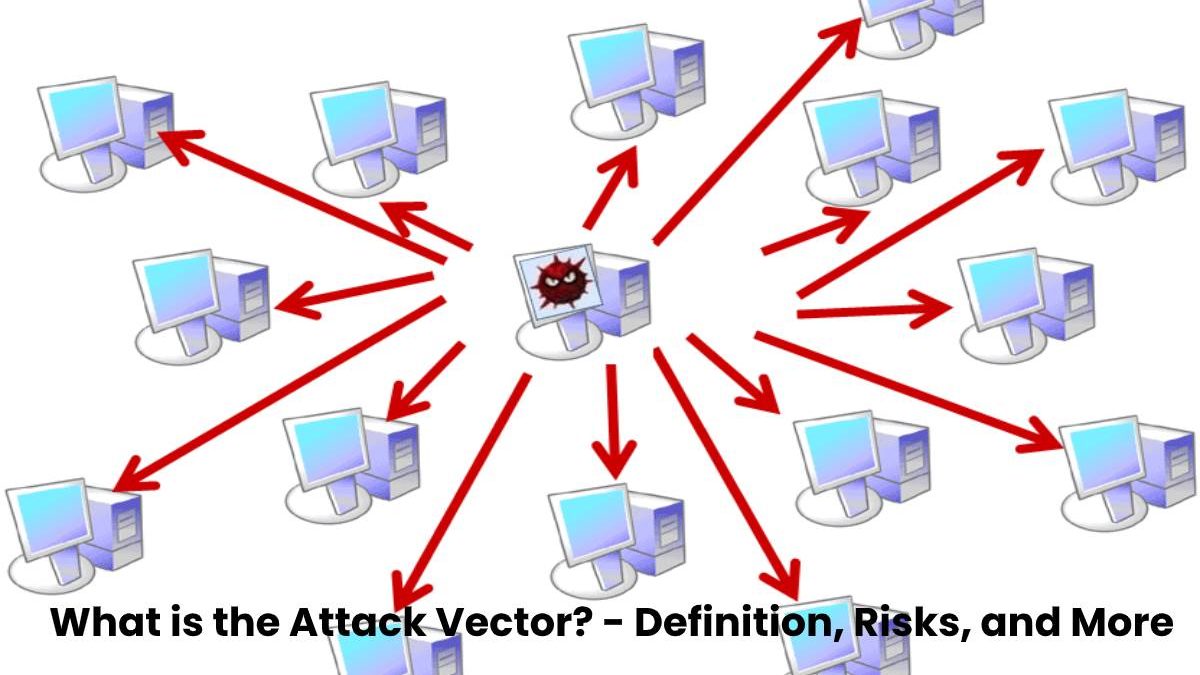
The attack vector describes the route of an attack and the technique used.
Cybercriminals use the attack vector to gain access to computers or servers in the network to install a virus or cause other damage.
And also, Attack vectors help attackers exploit the vulnerabilities in affected systems, including the human component.
Which attack vectors are there?
- Firstly, Common attack vectors include email attachments, viruses, websites, instant messenger messages, pop-up windows, and chat rooms.
- And also, The methods for the attacks require programming knowledge that need some hardware.
- Cyberterrorists are continuously improving their attack vectors and developing entirely new ways and techniques.
What are the attack vectors of a website?
Due to the constant development of applications and the use of new technologies, the threats to web applications are always changing.
And also, The OWASP (Open Wen Application Security Project) has worked out the top 10 risks for websites taking into account the attack vector, and technical impact:
1. Injection vulnerabilities
Firstly, Injection vulnerabilities pose a high risk, and cybercriminals can use SQL injection to make changes to the database and gain unauthorized access.
2. Errors in session management and authentication
If authentication and session management functions do not implement correctly, attackers can compromise the session token and password.
3. Cross-Site Scripting (XSS)
Basically, If an application accepts unchecked data and forwards it to a web browser without validation, it is an XSS vulnerability.
4. Unsafe direct object references
And also, If references to files, database keys or folders are accessible from the outside, dangerous direct object references occur.
5. Security-related misconfiguration
The configuration of the website must be correct, and this includes the configuration of the application, the framework used, the database server and the platform
6. Loss of confidentiality of sensitive data
If an application does not correctly protect confidential data such as credit card data, attackers can read, change or delete this insufficiently protected data.
7. Incorrect authorization at the application level
And also, In many applications, functions for different access rights are released simply by hiding the buttons in the user interface.
8. Cross-Site Request Forgery (CSRF)
With a CSRF attack, cybercriminals want to ensure that victims make a manipulated request in a web application that they already logged in.
9. Use components with known vulnerabilities
And also, In web applications, the frameworks and other software modules used usually accessed with full permissions.
10. Unchecked redirects and redirects
Redirects to other sites or other forms often made using untrustworthy data.
And also, The Top 10 of the OWASP only records the highest risks, but there are more dangers.